Have you fallen victim to a hack on your Mac? Perhaps one of these exploits can show you how.
I was contacted on Twitter by a very polite man who informed me that his security was breached remotely. He wasn’t sure how this happened exactly but provided this really interesting article that he though may shine some light on the situation. >ARTICLE<
Basically, it mentions that hackers are able to use a Rootkit (which is basically software that is designed to enable access to a computer where it should not be enabled and mask itself) to access the Mac in sleep mode. This could mean that he has a backdoor on his computer now that is very well hidden and could let the attacker come back at any time.
I took some time to put in some research, and I found this extremely interesting… But frankly scary page that lists exploits and rates how bad they are here: https://www.cvedetails.com/vulnerability-list/vendor_id-49/product_id-156/Apple-Mac-Os-X.html
I’m under the impression that most if not all of these are genuine.
For the average reader
You might open this and have no idea what any of those exploits mean. Well, it means IF you are being targeted one, or multiple of these may be used against you. So probably best to brush up on them.
My best advice to you would be that if you are doing anything that’s going to require you to delete your search history, then you should wear a virtual condom.
Virtual Machine baby!
A virtual machine is something you can download on your PC and as well as on your mac! (it’s just a little harder).
It will protect your actual computer from getting any type of virus or rat installed.
I don’t want to suggest any in specific because I think it’s best you find which one works for you.
In most cases
I think that in most cases exploits are localized, but remote ones can be just as bad.
It’s likely though that if you were infected it was because of careless use of the computer. I’m not here to scare you, the truth is that hackers just aren’t all that interested in Joe Blow who logged in to check out Jay’s blog and watch cat videos.
Back to the man who messaged me
I am a bit all over the place here, given it’s way past my bed time and I am turning into a pumpkin at this point.
He’s been doing research on what may have happened but he advises me that he finds it hard to understand some of the terminology that comes along with exploits. I want to take this time to simplify some of these terms in a way people who don’t know a lot about computers can understand.
TERMINOLOGY
#1 Phishing
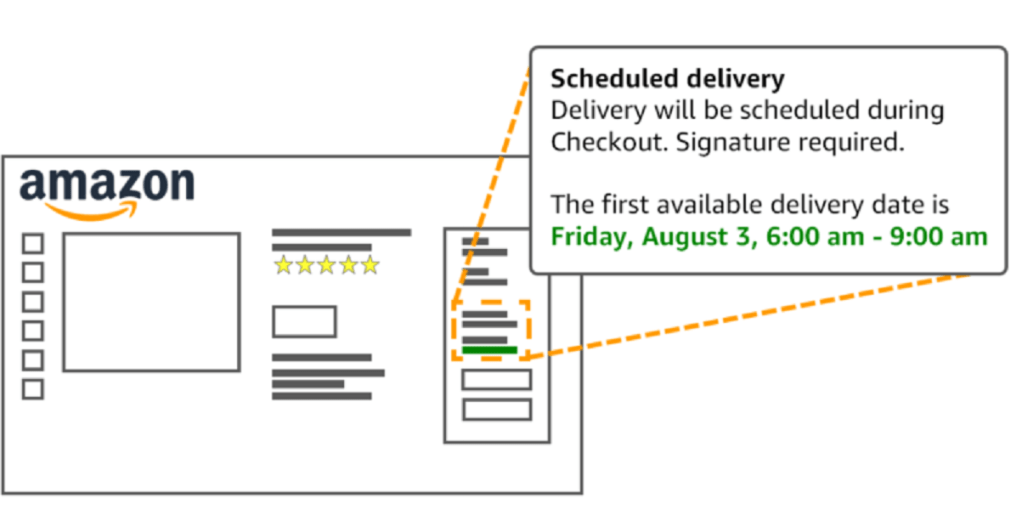
This is when a hacker poses as something legitimate, in an attempt to have you reveal personal information to them. It’s often done on a large scale.
They will for example send you an email asking you to login to your Amazon to win free money, only to direct you to a fake page that looks like Amazon, where it will record your login information.
#2 RANSOMWARE
This is a form of malware that is used to lock people out of their files by encrypting them. Often they will be asked money to have the files recovered. Which may or may not happen.
#3 SPOOFING
This is one I see people fall for time and time again unfortunately. It’s when someone makes their information seem like it’s coming from somewhere else when it’s not. So one might use an exploit to make it look like their email is amazonsupport@amazon.ca or whatever. It can get way more complex than that but that is a topic for another time.
#4 Brute Force Attack
This is basically exactly how it sounds. Often the attacker uses software that gains access to accounts by guessing the password / username with trial and error.
#4 DDOS
This is a Distributed Denial of service attack. This hacking terminology is highly common among hackers and is a major concern for website owners and developers. A DDoS attack is carried out with the aid of zombies or botnets controlled by black hats. By programming the botnets, the black hats command them to send data packets to the targeted web server from multiple systems. This floods the target server thereby slowing down or even crashing and shutting down the server thereby disrupting any activity. All the while the user of the server is oblivious to the attack.
#5 Payload
Essentially, a payload is a cargo of transmitted data over a network. However, in black hat hacking terminology, a payload refers to the part of the virus that performs malicious actions, such as compromising data, destroy information, or hijacking the computer system.
#6 Rat
Remote Access Tool or Remote Access Trojan (RAT) is a form of malware which can be operated by even an unskilled hacker. Once a RAT is installed on your system, the attacker gains complete control of the system. While RAT can be used for legitimate purposes, like when a user wants to access his home computer from another location, it is largely used for illegitimate reasons.
#7 Cloaking
Hackers often use Cloaking to present different content or URLs to human users and search engines, thereby cloaking them under legit looking web material. Hackers use dynamic scripts and .htaccess rules to hide their tracks by returning a 404 or 500 error code to certain IP addresses or browsers while serving spam to other IP addresses or browsers.
#8 Encryption / Decryption
The process of scrambling data or messages making it unreadable and secret. The opposite is decryption, the decoding of the message. Both encryption and decryption are functions of cryptography. Encryption is used by individuals as well as corporations and in digital security for consumer products.
#9 Opsec
OpSec is short for operational security, and it’s all about keeping information secret, online and off. Originally a military term, OpSec is a practice and in some ways a philosophy that begins with identifying what information needs to be kept secret, and whom you’re trying to keep it a secret from.
Very important this one, take it seriously.
#10 Worm
A specific type of malware that propagates and replicates itself automatically, spreading from computer to computer. The internet’s history is littered with worms, from the Morris Worm the first of its kind, and the famous Samy worm, which infected more than a million people on MySpace.
All this said, I hope that the importance of keeping yourself protected is becoming more important.
I’m going to end this article off here, but this blog is still in it’s infancy and I am always updating things. Keep updated with what I post by subscribing / following me on twitter.
If you have any questions, please comment below and I will answer them in this blog post for each of you.
Until next time & as always, stay safe.